XML Save/Load bug fix...
VARNA: Visualization Applet for RNA
A Java lightweight component and applet for drawing the RNA secondary structure
Overcoming Java's recently acquired taste for stupidity
This page describes several ways to work around the security error messages, which pop up anytime a VARNA applet is present on a page, and prevent Applet/WebStart versions of VARNA to operate on recent versions of Java.
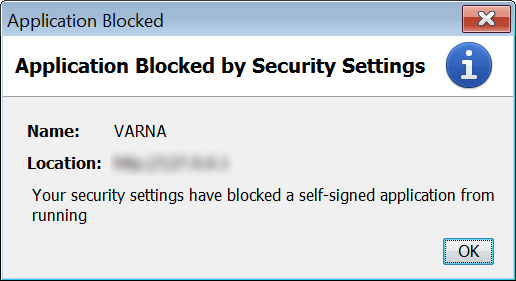
Why am I getting these messages?
This error message means that the authors of the downloaded code are unknown to a list of commercial companies that are deemed trustworthy by Oracle/Java (Verisign, Comodo, Thawte...). Despite what is stated in the misleading text, VARNA's code is signed by a third-party certificate issued by the French National Center for Scientific Research (Centre National de la Recherche Scientifique-CNRS). Despite arguably being one of the leading research institution in Europe, CNRS is unfortunately not one of the default certification authorities for Java, leading to VARNA's execution being refused.
Is it still safe to run VARNA?
Absolutely! As long as you download VARNA directly from the official site at http://varna.lri.fr, you are getting a malware/virus-free piece of software.
How to fix the issue and run VARNA?
In the long term, we will most likely purchase a commercial certificate.
Until then, the following procedures will allow you to run VARNA:
- (Preferred) Adding the CNRS certificate to JAVA's Trusted Signing Authorities:
- Download and save the CNRS base certificate
- Open the Java Control Panel (for mac users, for windows users)
- Select the security tab
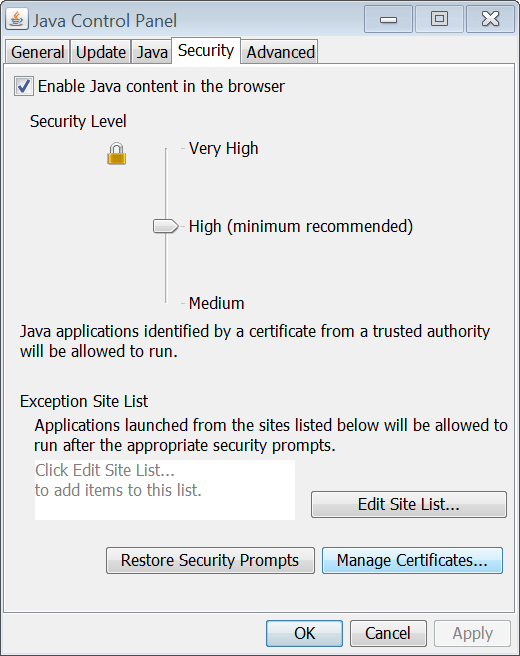
- Click the Manage Certificates button
- Switch to the Signer CA panel button
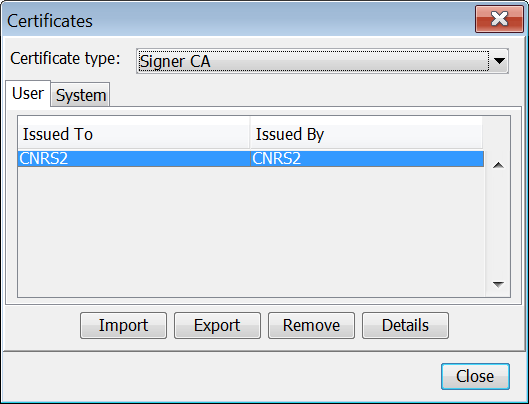
- Click the Import button, and locate/select the CNRS certificate saved in step 1.
- Close all instances of your browser, and relaunch it
- Open one of the VARNA pages and accept the confirmation message (you may want to check the Do not show again box to avoid further notifications)
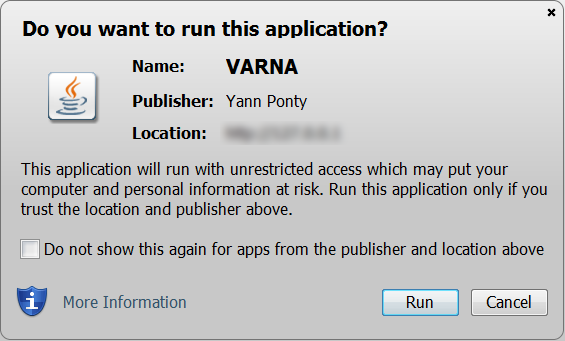
- Validate by clicking Run and voila...
- As a desktop (offline) application: Oracle's recent changes of their security policy does not affect (yet!) JAR files executed directly using the
java,javaw... executables. This means that one can download one of the JAR distributions of VARNA, and execute it directly as a Desktop application (by double clicking it from Explorer/Finder, or by running a command line of the sortjava -jar VARNAxxx.jar) - Weaken Java security settings (Baaaad!):
- In the Java Control Panel (for mac users, for windows users) set the security level of Java to medium and validate.
- Close all instances of your browser, and reopen it
- Accept the scary confirmation message
How did we get there?
In so many words, one could possibly summarize the situation as: Oracle screwed up big time, tried to make up for it, and unfortunately killed non-commercial Java projects in the process.
To elaborate a bit, Java and its current promoter Oracle have much suffered recently from the discovery of many security flaws (or exploits) in the Java virtual machine. Due to its perceived inability to diagnose and fix the severe security hole(s) in reasonable time, Oracle has jeopardized Sun's hard earned reputation for reliability and safety. For this reason, they were facing the very real prospect of losing many of its commercial (paying) customers, who would have been equally affected by the lack of reliability of the JVM, and the decreasing trust in Java-related products.
Consequently, Oracle took the decision to make it mandatory for applets to be signed by a third-party commercial partner. This decision was possibly based on the rationale that whoever can be identified can also be located, held accountable, and is therefore less likely to commit a felony in the first place (e.g. use one of the remaining holes in Java VM to hack an unsuspecting user). That way, they must have reasoned that they would regain some of their clients' trust, and further increase the competitive advantage of their commercial JAVA developers (the ones that can afford a third-party certificate).
This policy is so wrong and hurtful, and on so many levels, that I could rant for ages about this many paragraphs, so I'll try to keep it simple:
- A signed certificate does not ensure that the certicate owner is well-intentioned (or easy to locate), so this policy does not really increase the level of security experienced by the user
- Free open source (and/or academic) software projects simply don't have the kind of money required to get a commercial certificate, so this policy will restrict Java software to established commercial editors. This will likely lead to a descending vortex, where the lack of choice will limit the users' incentives to install the plugin, thereby limiting the incentives of editors to choose Java a their technology of choice, further limiting the supply of cool products for the users...







